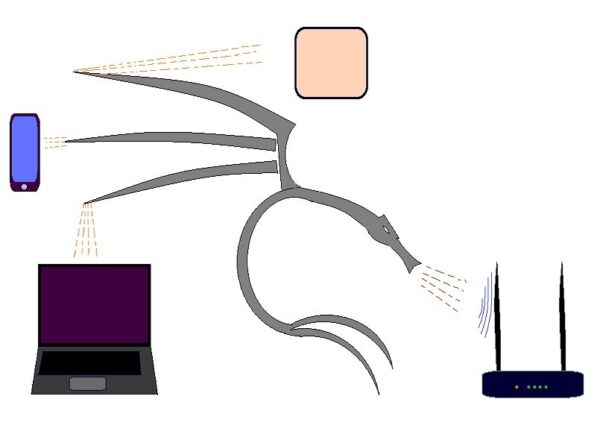
There are ways for you to feel more secure within your network. Just follow a few steps, and your can protect wireless from Kali Linux atacks and other hacking tools.
In fact, it is necessary protect wireless from Kali Linux, but it’s not just this OS that does the attacks. There are also many other tools that do the same thing and for which we do not know almost anything. Today, there is a chance that with an app downloaded on any SmartPhone with non official firmware, to cause problems in a wireless AP.
In fact Kali Linux it is designed to test security. But it is also used for malicious purposes.
Ok, let’s take some steps to protect Wireless AP and devices connected to it from Kali and other hacking tools.
For the moment we have only one device that we will use in our examples. We have a TP-Link AP.
- Enable AP isolation. This stops communication between the devices. Atackers use this opportunity to access through the client.
- A strong WPA password. A combination with letters, numbers and special characters is a strong password. This prevents Hydra and other tools to find a password.
- Enable Wireless Mac filter. Take care of this step. First you need to register Mac Addresses for the devices that are allowed to connect, otherwise you will lose the connection to your wireless. If a mac address is not registered, it can not be connected, even if he knows the WPA password.
- Enable SPI Firewall. You can activate or deactivate other services if you do not need them.
- Enable Dos Protection.
- Enable Device Management filter. Same as in Step 3. Carefully, you can lose management capability. You need to set up the Mac Address of the device that is allowed to control and configure the router (your wireless AP).
So this example was for a TP-Link wireless AP. The logical configuration method on other devices is the same.